Nova Prism Start 440-280-1985 Unlocking Contact Tracking
Nova Prism Start 440-280-1985 Unlocking Contact Tracking presents a data-driven framework for identifying and monitoring interactions within a defined network. It ingests diverse event streams, applies streaming joins and windowing, and maintains a current interaction graph with anomaly flags. Governance, consent, and auditable transformations are embedded, along with access controls and immutable audit trails. The approach balances real-time insight with privacy safeguards, offering measurable outcomes and prompting further consideration of implementation nuances. The next step reveals the practical implications and tradeoffs.
What Is Nova Prism Start 440-280-1985 Unlocking Contact Tracking
Nova Prism Start 440-280-1985 Unlocking Contact Tracking refers to a system or methodology designed to identify and monitor interactions between entities within a defined network.
This framework quantifies links, traces attribution, and assesses risk. It remains adaptable, emphasizing measurable outcomes rather than prescriptive narratives. The analysis notes an unrelated concept, an off topic idea, as a contextual curiosity.
How Contact Tracking Works in Real Time
Real-time contact tracking continuously ingests event streams from heterogeneous sources, correlating identifiers, timestamps, and spatial signals to construct an up-to-date interaction graph.
It supports streaming joins, windowing, and anomaly flags, presenting a coherent map of interactions.
Privacy controls and data lineage are embedded governance features, ensuring traceability, consent compliance, and auditable transformation without compromising analytic agility or freedom to explore insights.
Balancing Insight and Privacy: Access Controls and Audit Trails
Balancing insight and privacy hinges on disciplined access controls and robust audit trails that translate governance into actionable analytics.
The framework enforces least-privilege roles, enumerated permissions, and anomaly detection to sustain insight balancing without compromising data integrity.
Audit trails provide immutable, time-stamped records.
Privacy controls limit exposure, ensuring compliant data sharing while enabling rigorous, auditable analytics across organizational boundaries.
Practical Use Cases and Implementation Tips
Do practical use cases for contact tracking hinge on clearly defined data flows and measurable outcomes, or do they rely on adaptable architectures that maintain privacy while accelerating insight?
The analysis emphasizes privacy safeguards and data minimization, aligning with user consent issues and auditability.
Real time alerts, access controls, incident response, and compliance frameworks operationalize precision, with measurable risk reduction and transparent governance.
Conclusion
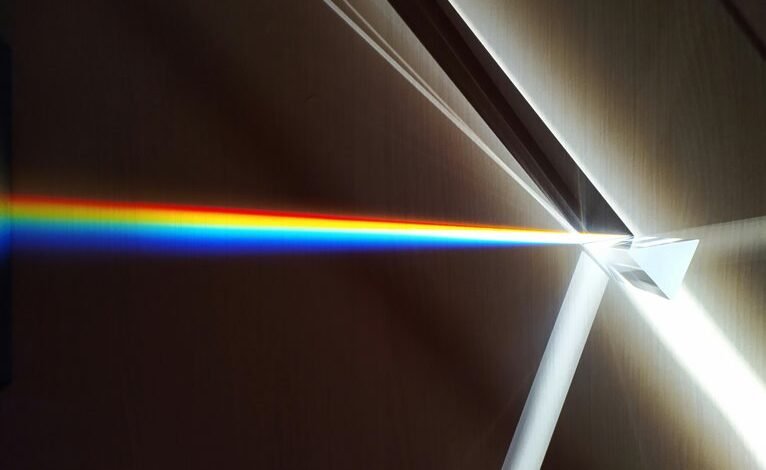
Nova Prism Start 440-280-1985 Unlocking Contact Tracking closes like a lighthouse, its beacon tracing every vessel through a fog of data. The graph of interactions gleams—nodes as satellites, edges as bridges—yet the harbor remains guarded by iron gates: access controls, immutable logs. In the glow of real-time joins, privacy anchors the course, and governance charts the tides. The system speaks in measured pulses, turning streams into actionable insights without surrendering the shoreline of consent.



